What is Sysjoker :
Το Sysjoker είναι ένα κακόβουλο backdoor λογισμικό που ανακαλύφθηκε για πρώτη φορά τον Δεκέμβριο του 2021 από την Intezer. Είναι εξελιγμένο και γραμμένο σε C++ .
Το Sysjoker είναι κακόβουλο λογισμικό πολλαπλών πλατφορμών που στοχεύει λειτουργικά συστήματα Windows, Linux και macOS. Συχνές επιθέσεις για το Sysjoker είναι συνημμένα email, κακόβουλες διαφημίσεις και μολυσμένο λογισμικό.
Το κακόβουλο λογισμικό Sysjoker αποτελεί μεγάλη απειλή επειδή μπορεί να συνδεθεί με εξελιγμένες επιθέσεις. Αυτές οι επιθέσεις μπορεί να είναι ransomware, εγκατάσταση crypto miners ή spyware.
Behavioural analysis :
Once Sysjoker infects a machine, it will start performing the following actions:
- Creating folders and files
- Establishing its presence
- Carrying out procedures for the discovery of other systems
- Hide in standby mode, waiting for commands.
Σε όλες τις πλατφόρμες, μετά την εκτέλεση του το Sysjoker, θα δημιουργήσει ορισμένους καταλόγους και θα μεταμφιεστεί ως ενημέρωση συστήματος.
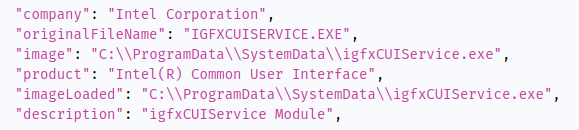
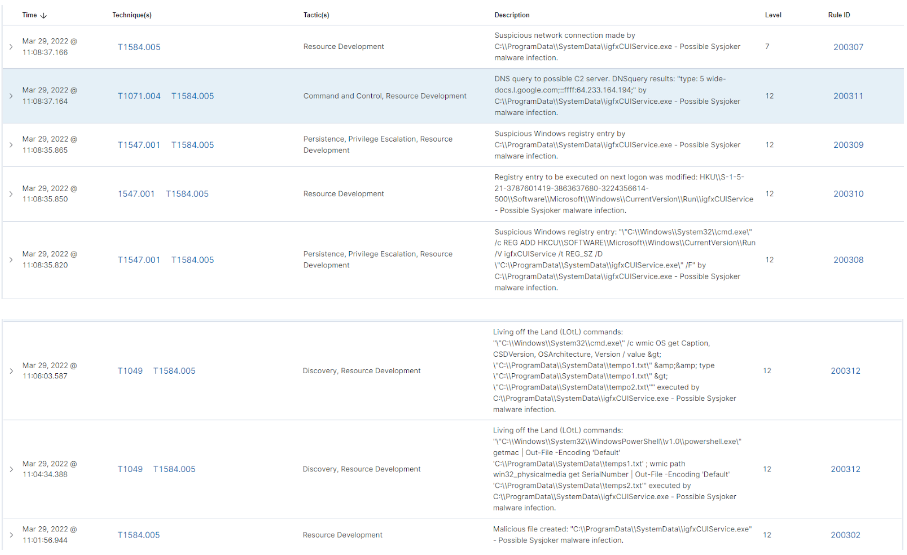
Στα Windows, μεταμφιέζεται ως μια πολύ γνωστή διεργασία Intel Common User Interface, igfxCUIService.exe.
Sysjoker will try to stabilize itself by various means depending on the operating system:
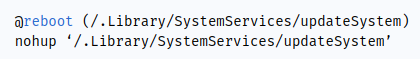
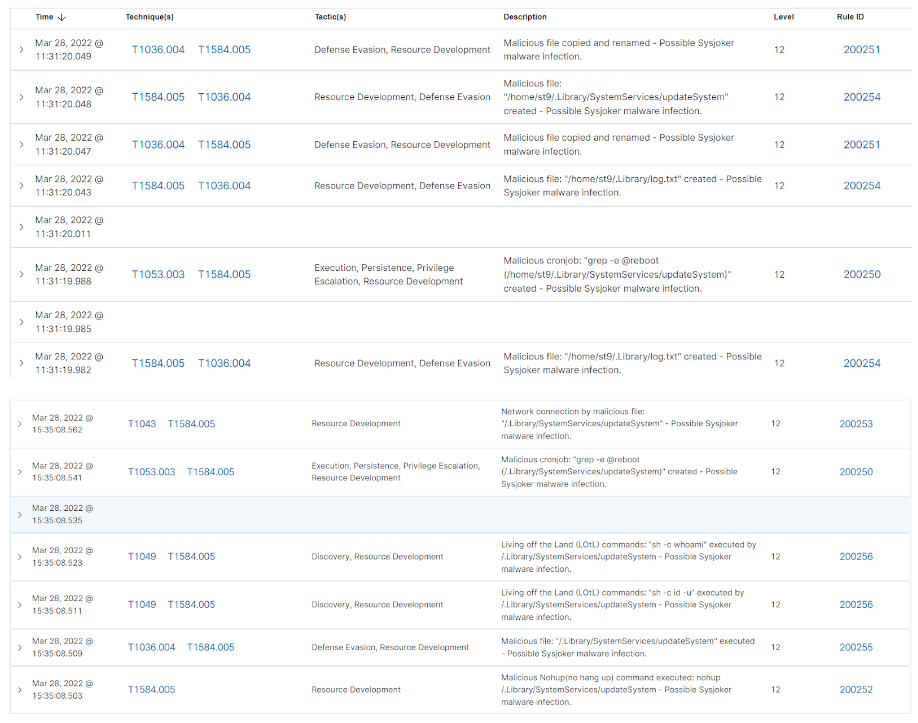
Linux/Unix : Runs a cron process and executes the nohup command.
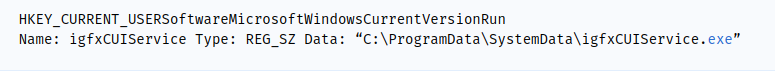
Windows : It is added to the list of Windows executables.
macOS : Creates a file in the LaunchAgents folder.
![]()
Στη συνέχεια, το Sysjoker θα εκτελέσει τις εντολές Living off the Land (LOtL) για να συγκεντρώσει πληροφορίες δικτύου και συστήματος σχετικά με το μολυσμένο μηχάνημα.
Χρησιμοποιεί προσωρινά αρχεία κειμένου στα μηχανήματα των Windows για να καταγράφει τα αποτελέσματα των εντολών Living off the Land (LOtL) και C2.
Μετά από όλες αυτές τις ενέργειες, το μολυσμένο μηχάνημα είναι έτοιμο να λάβει εντολές από τον διακομιστή C2.
Malicious files (HASH):
Then, Sysjoker will execute Living off the Land (LOtL) commands to gather network and system information about the infected machine. It uses temporary text files on Windows machines to log the results of LOtL and C2 commands. After completing these actions, the infected machine is prepared to receive commands from the C2 server.
Linux:
bd0141e88a0d56b508bc52db4dab68a49b6027a486e4d9514ec0db006fe71eed
d028e64bf4ec97dfd655ccd1157a5b96515d461a710231ac8a529d7bdb936ff3
Windows:
1ffd6559d21470c40dcf9236da51e5823d7ad58c93502279871c3fe7718c901c
61df74731fbe1eafb2eb987f20e5226962eeceef010164e41ea6c4494a4010fc
649a97980ed3eeed9a9b61eafd1d60c8d2d15c3be1d6acd3723af87fbda2e8fd
macOS:
1a9a5c797777f37463b44de2b49a7f95abca786db3977dcdac0f79da739c08ac
fe99db3268e058e1204aff679e0726dc77fd45d06757a5fda9eafc6a28cfb8df
d0febda3a3d2d68b0374c26784198dc4309dbe4a8978e44bb7584fd832c325f0
e83f6fdf04928cf1be0cec6c4c5a583561a06b5c18b559dc2298ae174709bf68
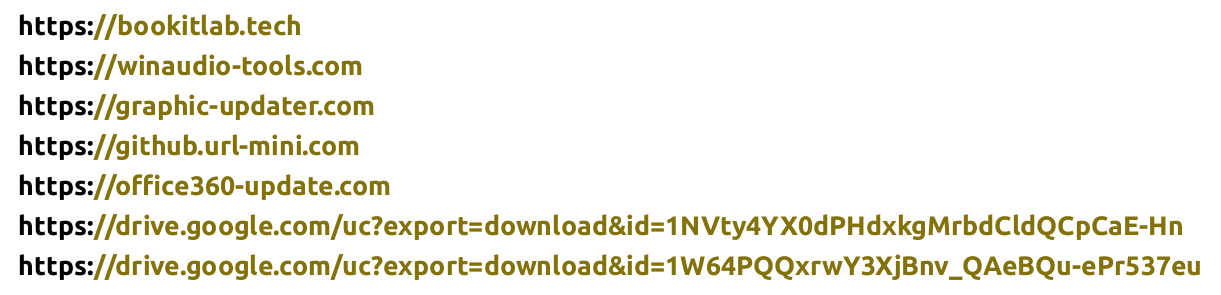
C2 domains :
These are the domains where the malware sends DNS requests and receives C2 commands:
Files and directories created after infection:
The following are the files and directories created by Sysjoker after it infects a computer:
Linux:
/.Library/
/.Library/SystemServices/updateSystem
/.Library/SystemNetwork
/.Library/log.txt
Windows:
C:\ProgramData\SystemData
C:\ProgramData\SystemData\igfxCUIService.exe
C:\ProgramData\SystemData\microsoft_Windows.dll
Several temporary files in the C:\ProgramData\SystemData directory
macOS:
/Library/MacOsServices
/Library/MacOsServices/updateMacOs
/Library/SystemNetwork
/Library/LaunchAgents/com.apple.update.plist
Locating Sysjoker:
Cyber Radar provides detection rules that will generate alerts when Sysjoker is detected on a machine.
Windows :
Cyber Radar logs events using sysmon
The System Monitor (Sysmon) is a Windows system service that monitors and records system activity in the Windows event log file. The capabilities of Sysmon include:
1) Detects files when they are created, deleted or changed and records the hashes of the files using SHA1 , MD5, SHA256 or IMPHASH.
2) Detects network connections and DNS queries
3) Logs when a new process is created or a process is terminated.
The image below shows some notifications about Sysjoker :
Linux /Unix :
To detect Sysjoker on Linux/Unix machines, Cyber Radar uses the following methods:
- SCA (Security Configuration Assessment): Cyber Radar SCA (Security Configuration Assessment) can be used to monitor system hardening and configuration policies and find ways to resolve any issues. We utilize SCA policy to scan the folder created after running Sysjoker.

- Auditd: Auditd is a framework that can be used for event monitoring on Linux/Unix systems. It can be utilized to monitor the folders and files created by Sysjoker. Additionally, we use Auditd to identify the cron job executed by Sysjoker.
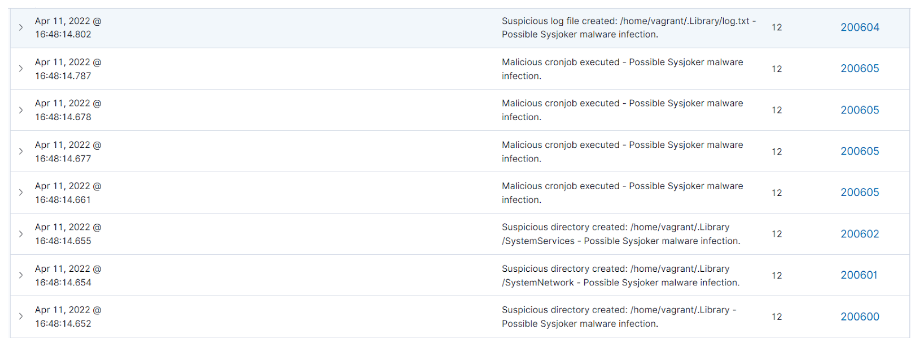
- SysmonForLinux: SysmonForLinux provides enhanced event monitoring capabilities, such as process monitoring, network connections, and file system changes. These events are then monitored by Cyber Radar, and if any suspicious activity related to Sysjoker is detected, the corresponding notification will be displayed.
Μην αφήσετε την ασφάλεια της επιχείρησής σας στην τύχη.
Επικοινωνήστε μαζί μας σήμερα για να δείτε πώς το Cyber Radar μπορεί να προστατεύσει τα δεδομένα και τη φήμη της εταιρείας σας. Μια επένδυση στην ασφάλεια της επιχείρησής σας είναι μια επένδυση για το μέλλον της.
Ανακαλύψτε περισσότερα ή ζητήστε ένα DEMO από εδώ: https://www.audax.gr/gia-epixeiriseis/cyber-radar-unified-xdr-siem-platform/