From the Audax Cybersecurity archive
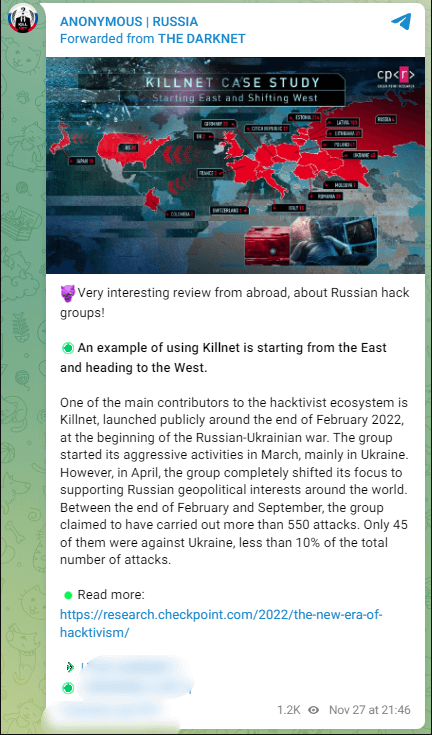
The ongoing conflict between Ukraine and Russia has attracted the attention of various cybercriminal groups and prompted them to engage in this cyberwar. Our research has shown us that over 190 hacking groups have been active during the Ukraine-Russia cyber war.
Some groups have aligned themselves with one of the two sides of the conflict and are using their skills to support their "favourite" country. KillNet is one such group that has played an important role and is known for its activities in DDoS attacks in favor of Russia.
Who is the KillNet team?
Killnet is a hacker group that supports Russia and is known for DDoS attacks against countries that support Ukraine, especially NATO countries, since the Russia-Ukraine war broke out last year. DDoS attacks are the main type of cyber attack that can cause thousands of connection requests and packets to be sent to the intended server or website per minute, slowing or even shutting down vulnerable systems.
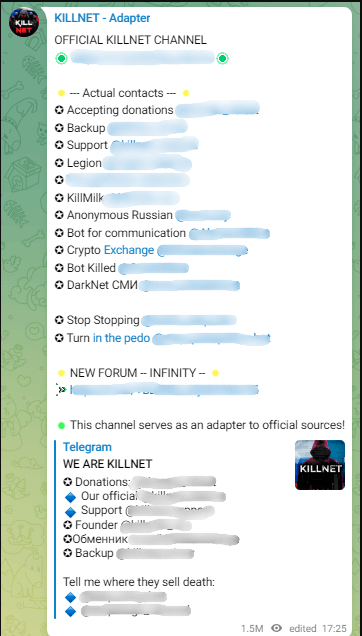
Although Killnet DDoS attacks usually do not cause much damage, they can cause service interruptions that last for several hours or even days. It is known that Killnet's founder, known as KillMilk, left the group in July 2022 and its new leader is a hacker using the pseudonym Blackside. However, KillMilk is still involved with the group and shares Killnet announcements on its official Telegram channel, titled "OFFICIAL KILLNET CHANNEL".
KliiNet_Audax Cybersecurity
KillMilk_Audax Cybersecurity
Killnet describe themselves as a group of hacktivists
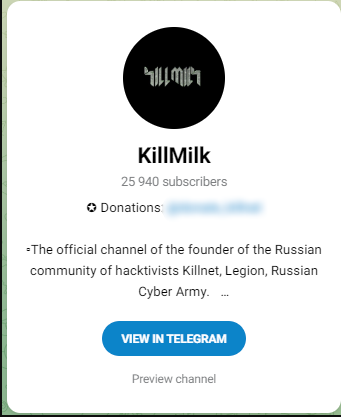
Until the war between Russia and Ukraine, Killnet was known as a DDoS attack tool that only subscribers could rent and use. With the crisis in Russia and Ukraine, Killnet emerged as a hacker group and continued its attacks under the name "Killnet".
Then the Killnet hacker group carried out many attacks to support Russia and fight for its interests. They attacked countries that supported Ukraine in the war between Russia and Ukraine. For months, the Killnet group attacked countries that support Ukraine and whose political interests are opposed to the Russian government.
They don't seem to be interested in financial gain. Their goal is to damage web services by disrupting them, mainly through DDoS attacks.
KillNet: History and Expansion
The group continue its operations for more than a year and has become a serious cyber threat. With the encouragement of users of the Killnet service, which reached tens of thousands of subscribers, they created subgroups under the name "Cyber Special Forces of the Russian Federation".
The group also started as another hacker group called LEGION in April 2022 and continued the DDoS attacks from there. Other groups under the LEGION group were also observed, each carrying out various attacks. In July 2022, the group announced that LEGION had been disbanded and would be restarted as LEGION 2.0. It is estimated that there are more than a thousand members of the group across all teams.
We Are KillNet_Audax Cybersecurty
Killnet said in a post on its Telegram channel that his birth date is November 13, 2021. However, they announced that they became a group of hacktivists on February 23, 2022.
Killnet's Relationship to Other Hacker Groups
A group previously known as XakNet announced that it has been integrated into Killnet, targeting critical infrastructure. Another group, later known as F**kNet, also expressed its intention to work with Killnet, targeting the public and private sectors in countries supporting Ukraine.
A former member of Killnet, who is now the leader of the Zarya group, also said that other hacker groups are working alongside them and defending Russia's interests, in an interview. He mentioned groups such as XakNet, Beregini, CyberArmy, Anonymous Russia, RaHDit, DPR Joker, NoName057 and Zsecnet.
The hacker also said that Anonymous Russia and the Zarya group were founded by hackers who left the Killnet group. Other hackers also joined Zarya from Killnet.
In the same interview, the leader of Zarya also explained the reason behind the creation of small groups dividing Killnet. The Zarya leader explained that creating small teams has its advantages. It is easier to manage a small group and it is harder for the enemy to understand who to attack. He also revealed that Zarya previously belonged to the Killnet group, but now operates as an independent entity.
Anonymous Russia_Audax Cybersecurity
KillNet: Objectives and Cyber Operations
Killnet has attacked many European and Western countries, including Ukraine, since February 2022. These include the United States, the United Kingdom, Germany, Italy, Romania, Lithuania, Estonia, Poland and the United Kingdom. It is worth mentioning the attacks on US airports, the Eurovision contest website and more than a thousand websites in Lithuania. There have also been attacks on railways and government gates in the Czech Republic.
Killnet has targeted several countries and has conducted operations since February 2022. Some of the notable targets and operations include:
- Ukraine: Killnet has carried out cyber attacks against Ukraine, targeting its government, infrastructure and websites.
- United States: The group has attacked US airports, aiming to disrupt travel and cause disruption.
- United Kingdom: Killnet has targeted websites and online platforms in the UK, with the aim of disrupting services and causing disruption to individuals and businesses.
- Germany: The group has carried out cyber-attacks on German targets, with the possible aim of disrupting critical infrastructure or compromising sensitive information.
- Italy: Killnet has targeted Italian websites and online platforms, with the possible aim of disrupting services and causing disruption.
- Romania: The group has carried out cyber attacks on Romanian targets, with the possible aim of disrupting critical infrastructure or compromising sensitive information.
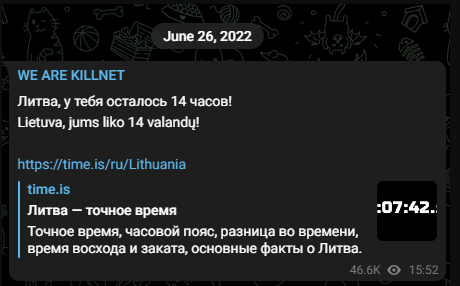
- Lithuania: Killnet has targeted over a thousand websites in Lithuania, with the possible aim of disrupting internet services and causing disruption.
- Estonia: The group has carried out cyber-attacks on Estonian targets, with the possible aim of disrupting critical infrastructure or compromising sensitive information.
- Poland: Killnet has targeted Polish websites and online platforms, with the possible aim of disrupting services and causing disruption.
These operations are conducted by DDoS (Denial of Service) attacks against government authorities, critical infrastructure, websites and web platforms in these countries. DDoS attacks cause thousands of connection requests and packets to be sent to the intended server or website per minute, slowing or even shutting down vulnerable systems.
Killnet attacks aim to cause disruption and interfere with services and systems for hours or even days. These attacks have affected the government, economy and social sector of the affected countries.
It is important to note that these attacks do not cause loss or leakage of data, but have serious consequences for the smooth functioning of systems and services, causing disruptions and malfunctions that affect access to services, communication and information exchange. These attacks can cause economic losses, loss of citizens' trust and damage the social functioning of countries.
Killnet attacks also target critical infrastructure such as airports, railway systems and government gateways. This results in disruption of daily operations, delayed travel and cybersecurity breaches.
Killnet attacks reveal their ability to affect the systems and services of large countries and cause disruption on a global scale. Their continued activity and cooperation with other attack groups demonstrates the serious risk facing affected countries and organisations. In April 2022, Killnet focused exclusively on supporting Russia's geopolitical interests globally. They reportedly carried out more than 550 attacks from the end of February to September. Only 45 of these attacks were directed against Ukraine, less than 10% of the total number of attacks.
Killnet attacked Romanian government websites.
They attacked Italy and managed to block some websites, while the attack on the CSIRT website was not successful. Killnet hacked the websites of the Istituto Superiore di Sanità and the Automobile Club of Italy during the same attack. The website of the Italian Screenwriters' Corps was also compromised and shut down for an hour. The attack was not as devastating as predicted.
June 2022:
The group targeted organisations in Norway through various DDoS attacks. The group also claimed responsibility for a DDoS attack through the Lithuanian government and private organisations.
Lithuania_Audax Cybersecurity
August 2022:
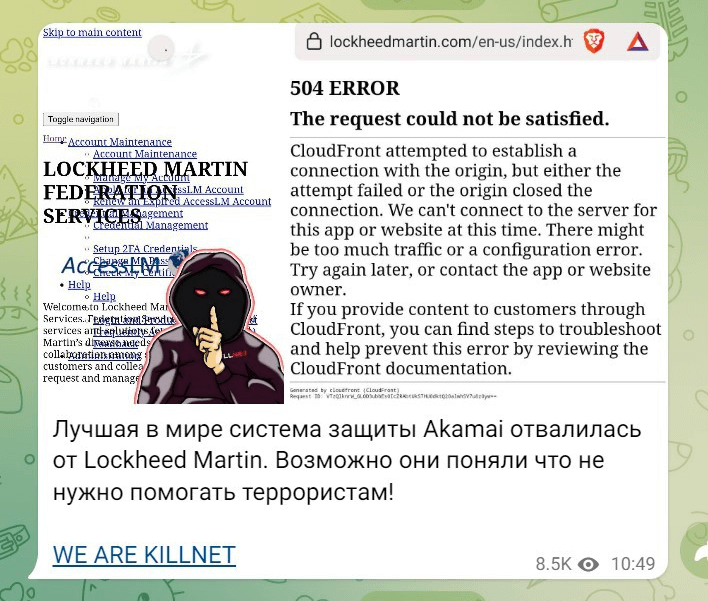
The group and its founder, called "KillMilk", claimed responsibility for a cyber-attack on the US defence company Lockheed Martin in retaliation for the HIMARS systems provided by the United States to Ukraine.
Lockheed Martin_Audax Cybersecurity
September 2022:
Killnet announced that it attacked 23 websites from 4 ministries and agencies in Japan, including e-Gov, a website portal for administrative information managed by the Digital Agency, and eLTAX, a website for local taxes managed by the Ministry of Internal Affairs and Communications.
October 2022:
Many airport websites in the United States were attacked.
Killnet has published a list of several government websites it intends to attack in the coming days, under a picture of a nuclear explosion behind the Statue of Liberty.

USA_Audax Cybersecurity
Possible targets are listed below:
Alabama
Alaska
Connecticut
Colorado
Delaware
Florida
Hawaii
Idaho
Indiana
Kansas
Kentucky
Mississippi
November 2022:
On Killnet's Telegram channel, the group shared a post that said: "We have gained power and are now able to reduce the traffic of drug addicts to the sellers' sites to zero! Not without your help, of course, comrades!"
Killnet's menacing perpetrators had hacked the largest Russian dark web site for drugs. They published data on sellers and drug addicts, storage locations, etc.
In an email from an employee of the Latvian Revenue Agency, they announced that they have VPN access to government corporate networks and have downloaded 200 gigabytes of files.
The Killnet hacker group announced that they attacked websites of Western governments and companies.
The White House announced that it has temporarily shut down its official website and Starlink its API. Experts said it is a major target because the Ukrainian military uses Starlink.
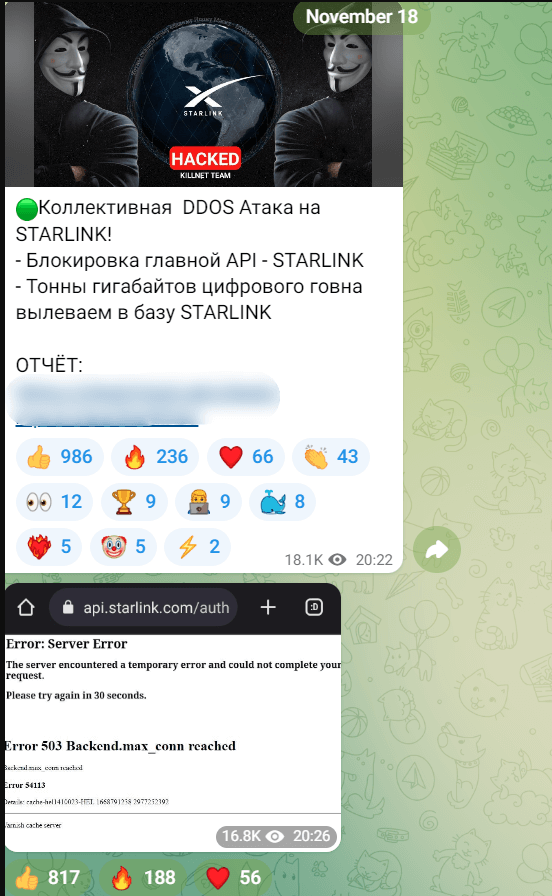
StarLink_Audax Cybersecurity
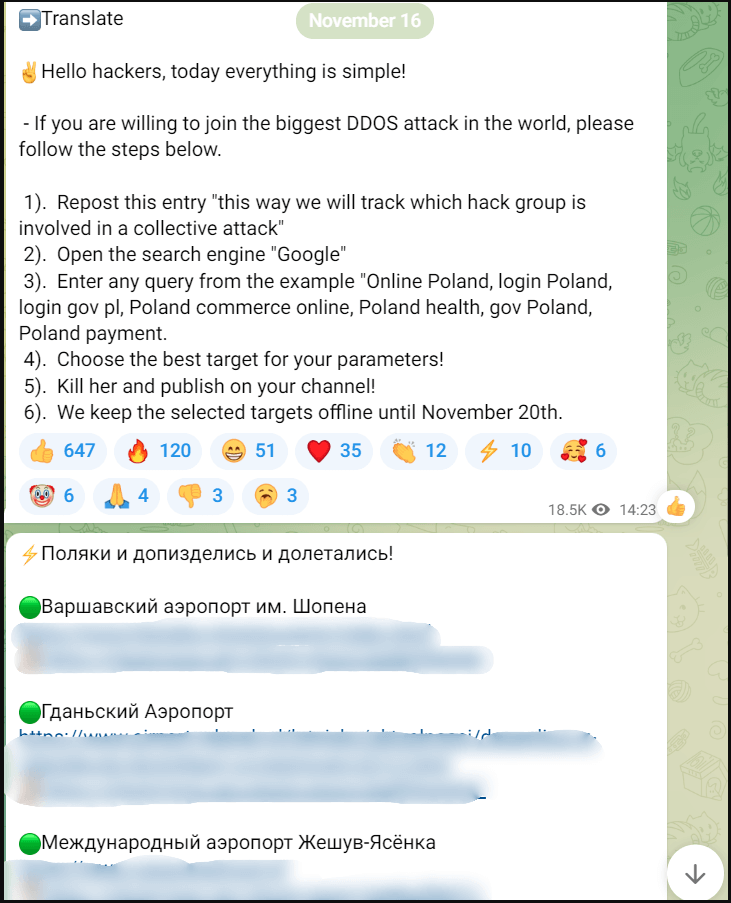
Killnet posted an announcement on its Telegram channel, asking all hackers to help attack Poland. They stated that several of the targets would have to stay "down" for several days. Following this announcement, the airports of Warsaw, Gdansk and Rzeszow fell victim to cyber attacks.
CyberOPS_Audax Cybersecurity
Δεκέμβριος 2022:
In a post, the Killnet group mentioned a new cyber operation called Infinity. They plan to launch this operation sometime this winter-spring, which is described as very dangerous.
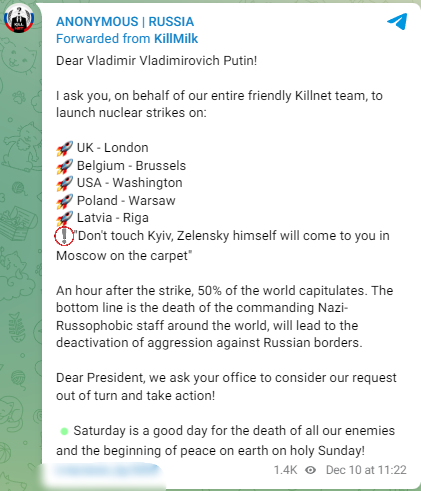
They have also published a post on their Telegram channel, calling on President Putin to launch nuclear attacks on the capitals of Ukraine's allies:
Nuclear_Audax Cybersecurity
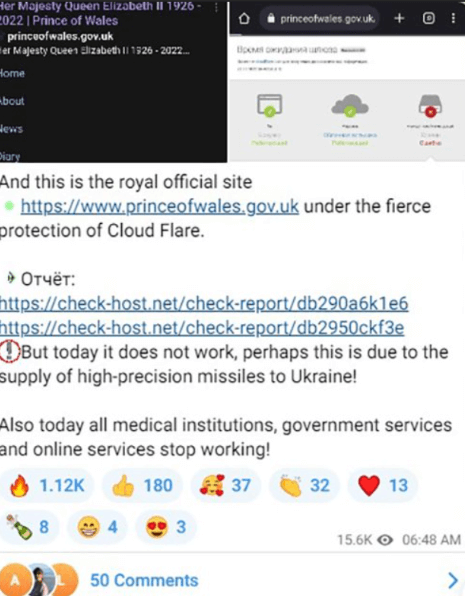
Another important piece of information about the Killnet group is that some members said they attacked the Bankers Automated Clearing Service (BACS), the London Stock Exchange and the official website of the Prince of Wales. Killnet reported that the "official royal family website" was not working. "Perhaps this is due to the supply of high precision missiles to Ukraine," the group said.
Wales Royal Website_Audax Cybersecurity
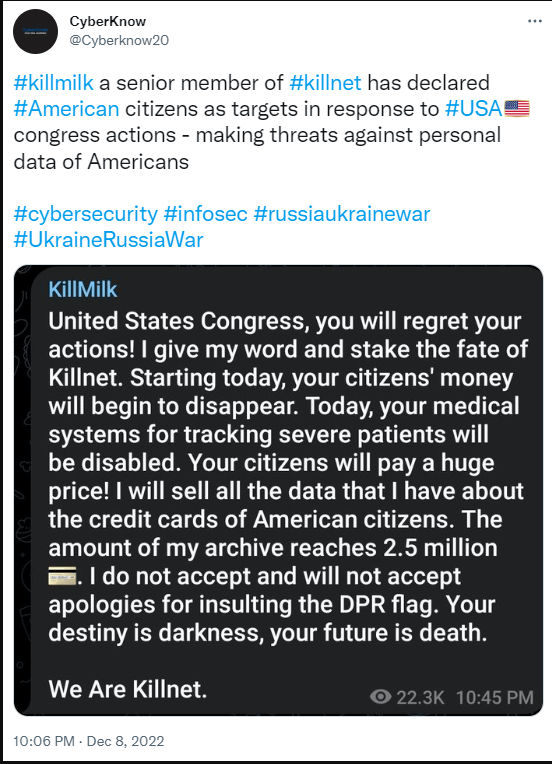
Killmilk, a high-ranking member of the Killnet group, has threatened the United States Congress with the sale of the health and personal data of the American people because of the politics of Ukraine by the United States Congress.
KillMilk_Audax Cybersecurity
January 2023:
In late January 2023, KillNet announced that it was targeting Germany via the Passion Botnet with the hashtag #ГерманияRIP.
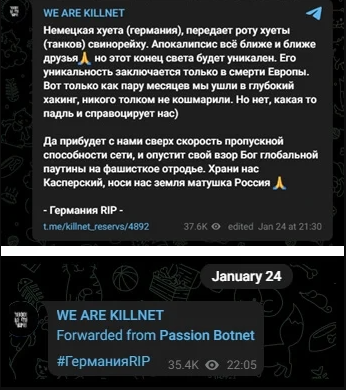
Germany_Audax Cybersecurity
A day after the announcement, the group published screenshots showing that they blocked access to several German websites, including the German Parliament (Bundesregierung) and the Federal Ministry of the Interior (Bundesministerium des Innern und für Heimat).
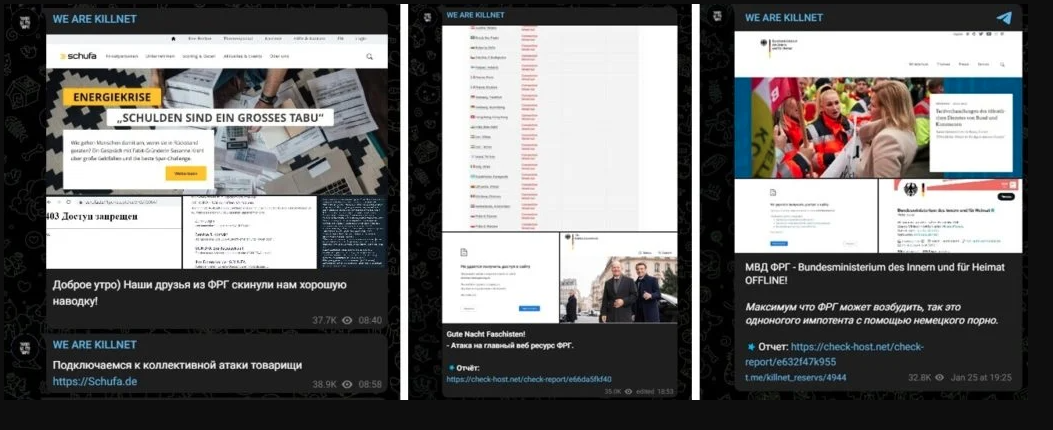
Germany2_Audax Cybersecurity
Killnet published a list of other German websites attacked on the same day, categorized by industry.
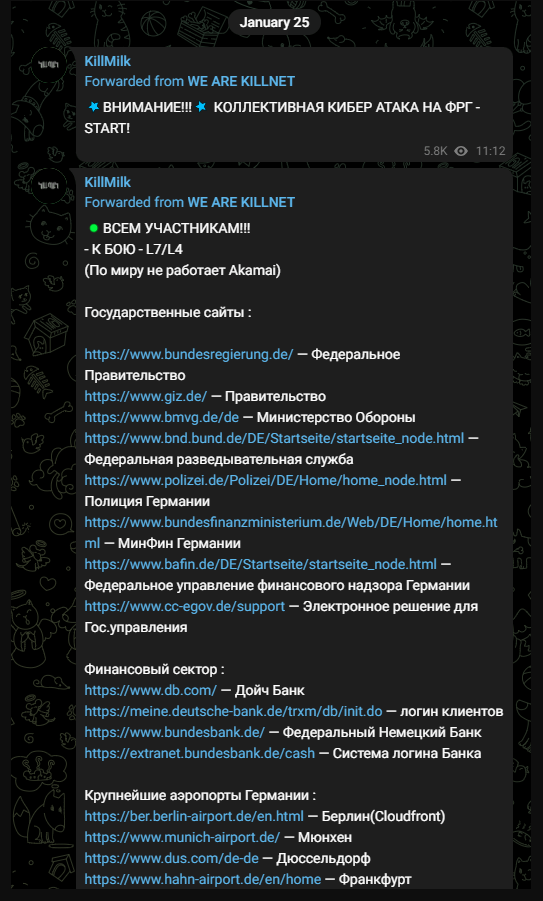
Germany3_Audax Cybersecurity
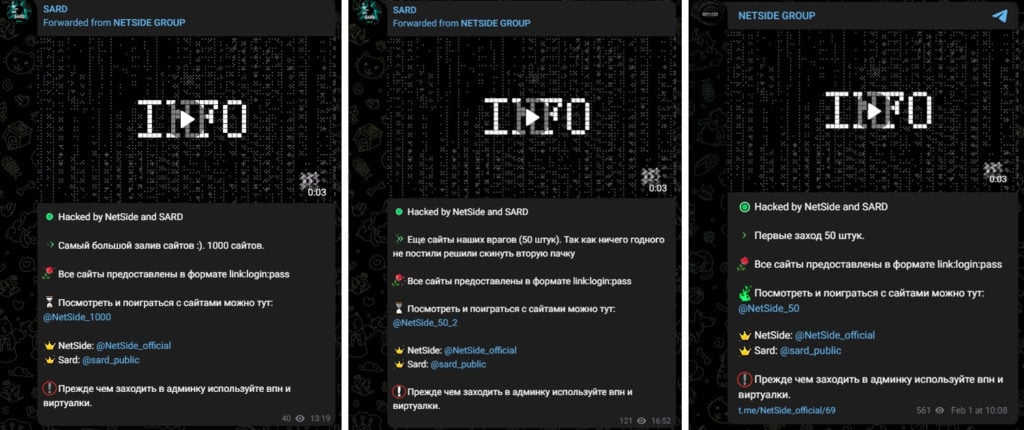
The NetSide and SARD groups on Telegram announced that they have hacked the admin panels of hundreds of websites to support Killnet and published the credentials on the Killnet page.
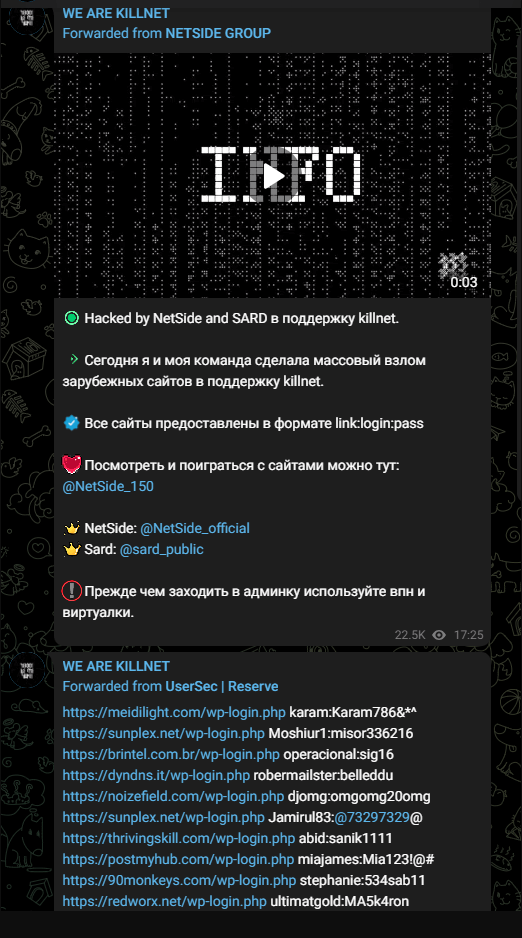
Hacking_Audax Cybersecurity
It is worth noting that NetSide and SARD make such postings on a regular basis.
killnet 9_Audax Cybersecurity
At the end of the month, Killnet said it carried out a massive Layer 7 DDoS attack on several healthcare organizations across the US. In addition, according to the Daily Mail, hospitals in the Netherlands were reported to have suffered a DDoS attack by Russian hacker groups.
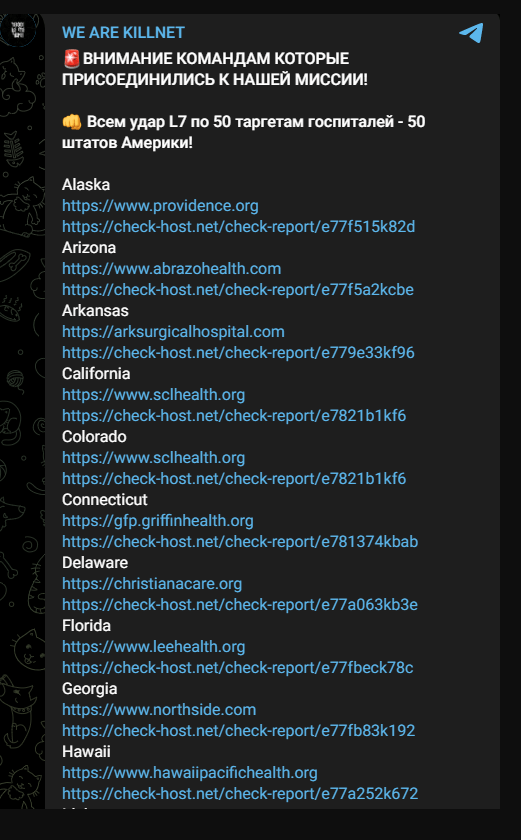
KillNet10_Audax Cybersecurity
February 2023:
February started with an astonishing announcement and a call to action. Killnet released a notification message encouraging anyone interested in attacking the United States to contact the administrator of the hacker group Infinity.
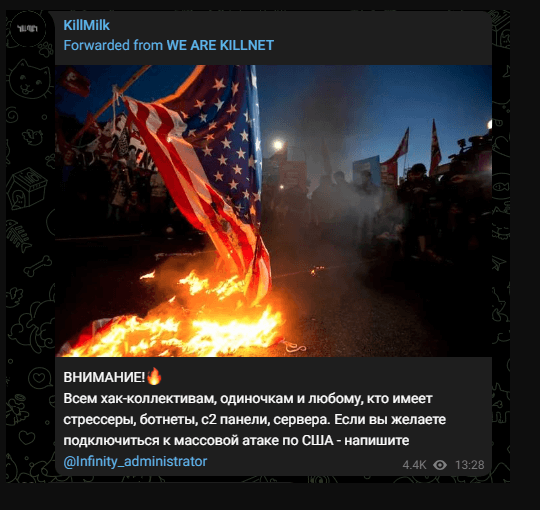
HackUSA_Audax Cybersecurity
KillNet targeted at Hospitals
From January 2023 onwards, Killnet is actively attacking healthcare organisations. In their Telegram post, they state that many hospitals' websites were down and that this attack was a joint operation.
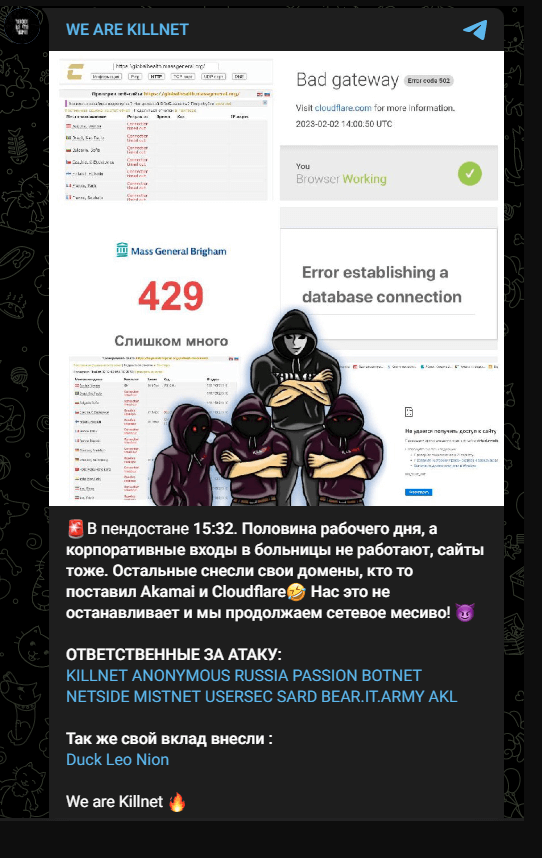
Some of those mentioned in KillNet's Telegram post are hacker groups, while some are known as DDoS-as-a-Service providers.
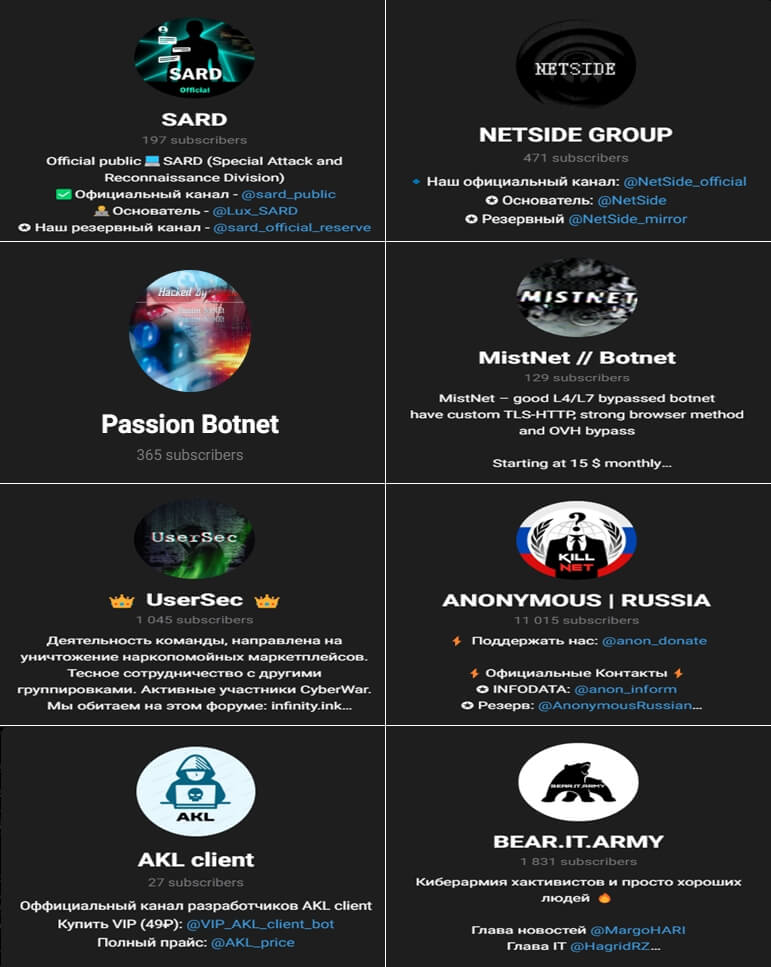
Killnet was recently observed operating with the Passion Botnet, a group offering DDoS-as-a-Service. The origin of Passion is unknown, but it has recently become more active, especially in early 2023. It has a history of targeting individuals and organizations against Russia's invasion of Ukraine, using techniques such as tampering and denial of service.
Also, other groups affiliated with Killnet offer the DDoS-as-a-Service model, such as AKL Client, Infinity Stresser and MistNet.
Killnet's partnership with several DDoS-as-a-Service providers may suggest that it will be more active in future events.
Prominent Characteristics & TTPs
Looking at Killnet's attacks and behaviour to date, some estimates can be made,
Because of their determination to defend Russia, the group chooses its targets among NATO-affiliated countries. They are also a potential threat to countries whose political interests are opposed to Russia's. They prefer DDoS attacks against their targets. Victims can recover from attacks, which usually last 1-3 days, with appropriate measures within hours. They target the websites of governments or public organizations. In doing so, they believe they are sending victims the message that they have chosen the "wrong side".
Ανακοινώνουν τις επιθέσεις και τους στόχους τους σε κανάλια του Telegram. Ο Killnet συνδέεται επίσης με άλλες ομάδες χάκερ που έχουν κοινούς στόχους με αυτούς ή δρουν στα ρωσικά συμφέροντα. Έχουν συνεργαστεί με τις ομάδες XakNet και F**kNet, καθώς και με τους προαναφερθέντες απειλητικούς παράγοντες.
MITRE Map
| Reconnaissance | Resource Development | Credential Access | Impact |
| T1595: Active Scanning | T1583: Acquire Infrastructure | T1110: Brute Force | T1498: Network Denial of Service |
| T1589: Gather Victim Identity Information | T1584: Compromise Infrastructure | T1489: Service Stop |
Main Tactics of Killnet
Brute-force attacks against:
- SSH (port 22) with the root account as the main target
- Minecraft and TeamSpeak servers
DDoS attacks on the OSI model:
- level 4 (SYN flood attacks)
- level 7 (high-capacity POST/GET requests) to cause resource exhaustion and system failure.
In various Telegram groups, they work with members using IP stresser-for-hire tools such as Crypto Stresser, DDG Stresser, Instant-Stresser and Stresser.ai. In addition, several scripts are used during their attacks. Some of them are CC-attack, MDDoS, Low Orbit Ion Cannon (LOIC), KARMA and Dummy.